Dumping Movable (nimhax)
如果有疑问并且懂英语的话,可以到 Nintendo Homebrew Discord 服务器上使用英文寻求帮助。(请注意,如果你身处中国大陆,你可能需要通过科学上网来访问 Discord)
你也可以到译者的 QQ 群寻求帮助,群号为 942052497。
如果你喜欢我们的教程,可以通过捐赠支持我们。
技术细节(选看)
为了在你的主机上安装 boot9strap,我们需要获得你主机上的唯一加密密钥。 To accomplish this, we use the Homebrew Launcher to launch nimhax and dump the data encryption key (movable.sed) from your device.
For a more technical explanation, see here for information about the nimhax exploit.
你需要准备点啥?
- The latest release of nimhax (the nimhax
.zipfile)
操作步骤
第一步 – 准备工作
- 将主机关机
- 将你的 SD 卡插入到电脑
- Copy the
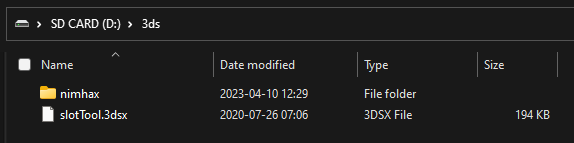
nimhaxfolder from the nimhax.zipto the/3ds/folder on your SD card - 将 SD 卡重新插入你的主机
- 启动你的主机
Section II - nimhax
- Open the Homebrew Launcher through your method of choice (likely the Internet Browser)
- Launch nimhax from the list of homebrew
- If the exploit was successful, a
movable.sedfile will appear on the root of your SD card
Next step: Frogtool
Once you have your device’s encryption key (movable.sed), you can use it in conjunction with Frogtool, which uses your movable.sed file to inject and take advantage of JPN Flipnote Studio.
While this method is faster, it requires downloading a file with a torrent client. Do not follow this method if you’re unable to use a torrent client.
Continue to Installing boot9strap (Frogtool)