BannerBomb3
Technical Details (optional)
To launch custom code, we exploit a flaw in the DSiWare Data Management window of the Settings application.
To accomplish this, we use your system’s encryption key (movable.sed) to build a DSiWare backup that exploits the system.
For a more technical explanation, see here.
相容性資訊
這些操作在美、歐、日、韓版可用,可透過系統版本號末尾的 「U、E、J、K」 字元來辨別。
如果您的主機為台灣版主機(系統版本號以 T 結尾的主機),請見此頁面。
必備項目
- Your
movable.sedfile from completing Seedminer or nimhax
第一節 — 準備工作
In this section, you will copy the files needed to trigger the BannerBomb3 exploit onto your device’s SD card.
- 關閉您的主機
- 將 SD 卡插入至電腦中
- Open Bannerbomb3 Injector on your computer
- Upload your movable.sed using the “Choose File” option
- Click “Build and Download”
- This will download an exploit DSiWare called
F00D43D5.binand a payload calledbb3.bininside of a zip archive (DSIWARE_EXPLOIT.zip)
- This will download an exploit DSiWare called
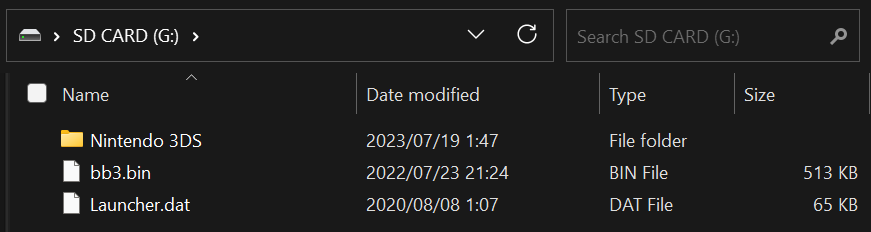
- Copy
bb3.binfromDSIWARE_EXPLOIT.zipto the root of your SD card- 「SD 卡的根目錄」指的是你的 SD 卡含有 Nintendo 3DS 資料夾的目錄,而非該資料夾內部
- This file does not need to be opened or extracted
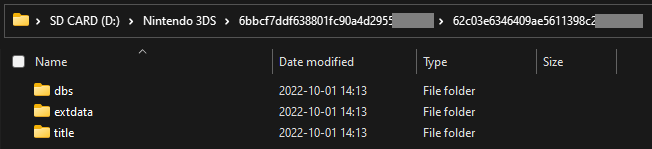
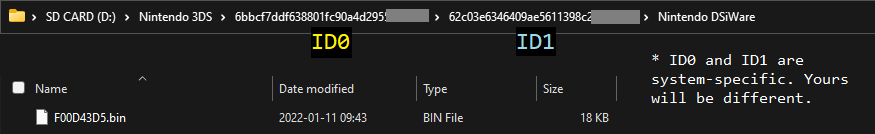
- Navigate to
Nintendo 3DS-><ID0>-><ID1>on your SD card - Create a folder named
Nintendo DSiWareinside of the<ID1>- If you already had the folder and there are any existing DSiWare backup files (
<8-character-id>.bin) inside, copy them to your PC and remove them from your SD card
- If you already had the folder and there are any existing DSiWare backup files (
- Copy the
F00D43D5.binfile fromDSIWARE_EXPLOIT.zipto theNintendo DSiWarefolder
第二節 — 按鍵檢查
In this section, you will see whether your shoulder buttons are working on your device. This will determine which method you will follow on the next page.
- 啟動您的主機
- Once you see the HOME Menu, press the (Left Shoulder) and (Right Shoulder) buttons at the same time
- The camera applet should appear
- 關閉您的主機
Next steps: Choose an exploit
If the camera appeared in the previous section, Safe Mode is likely to be working on your device.
If the camera appeared, continue to Installing boot9strap (USM)
If the camera did NOT appear, continue to Installing boot9strap (Fredtool)