Installing boot9strap (USM)
Technical Details (optional)
In order to exploit the SAFE_MODE firmware of our system, we need to inject an exploited WiFi profile.
We can do this using an existing exploit, BannerBomb3.
To accomplish this, we use your system’s encryption key (movable.sed) to build a DSiWare backup that exploits the system in order to inject the exploited WiFi profile into your connections list.
Once the WiFi profile has been injected, we will use SAFE_MODE, which is a recovery feature present on all 3DS consoles, to activate the exploited WiFi profile.
For a more technical explanation, see the following links for information on the BannerBomb3 and unSAFE_MODE exploits: BannerBomb3, unSAFE_MODE.
Compatibility Notes
These instructions work on USA, Europe, Japan, and Korea region consoles as indicated by the letters U, E, J, or K after the system version.
If your (Right/Left Shoulder), (D-Pad Up), or (A) buttons do not work, you will need to follow an alternate branch of Seedminer. For assistance with this matter, join Nintendo Homebrew on Discord and ask, in English, for help.
What You Need
- The latest release of SafeB9SInstaller (direct download)
- The latest release of boot9strap (direct download)
- The latest release of Luma3DS (the Luma3DS
.zipfile) - usm.bin (direct download)
Section I - Prep Work
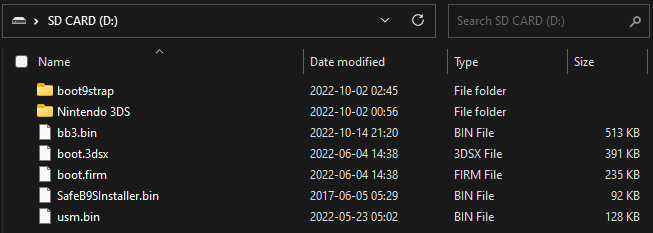
In this section, you will copy the files needed to trigger the unSAFE_MODE exploit onto your device’s SD card.
- Your SD card should be inserted in your computer
- Copy
usm.binto the root of your SD card - Copy
boot.firmandboot.3dsxfrom the Luma3DS.zipto the root of your SD card- The root of the SD card refers to the initial directory on your SD card where you can see the Nintendo 3DS folder, but are not inside of it
- Create a folder named
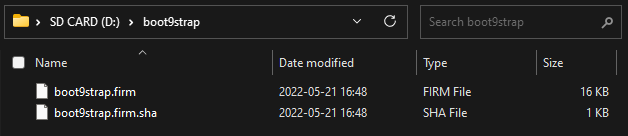
boot9strapon the root of your SD card - Copy
boot9strap.firmandboot9strap.firm.shafrom the boot9strap.zipto the/boot9strap/folder on your SD card - Copy
SafeB9SInstaller.binfrom the SafeB9SInstaller.zipto the root of your SD card
Section II - BannerBomb3
In this section, you will trigger the BannerBomb3 exploit using the DSiWare Management menu, which can be used to overwrite your Wi-Fi slots with hacked data. Your Wi-Fi connection settings will be temporarily overwritten while the exploit is active.
- Reinsert your SD card into your device
- Power on your device
- Launch System Settings on your device
- Navigate to
Data Management->DSiWare->SD Card(image)- Your device should show the BB3 multihax menu
- If this step causes your device to crash, follow this troubleshooting guide
- If the BB3 multihax menu says “cfw installed already”, you already have custom firmware and should continue from here
- Use the D-Pad to navigate and press the (A) button to select “Install unSAFE_MODE”
- Your device will automatically power off
Section III - unSAFE_MODE
In this section, you will enter Safe Mode (a feature available on all 3DS family devices) and navigate to a menu where unSAFE_MODE will be triggered, which will launch you into the boot9strap (custom firmware) installer.
- With your device still powered off, hold the following buttons: (Left Shoulder) + (Right Shoulder) + (D-Pad Up) + (A), and while holding these buttons together, power on your device
- Keep holding the buttons until the device boots into Safe Mode (a “system update” menu)
- Press “OK” to accept the update
- There is no update. This is part of the exploit
- Press “I accept” to accept the terms and conditions
- The update will eventually fail, with the error code
003-1099. This is intended behaviour - When asked “Would you like to configure Internet settings?”, select “Yes”
- On the following menu, navigate to
Connection 1->Change Settings->Next Page (right arrow)->Proxy Settings->Detailed Setup(image) - If the exploit was successful, your device will have booted into SafeB9SInstaller
Section IV - Installing boot9strap
In this section, you will install custom firmware onto your device.
- When prompted, input the key combo given on the top screen to install boot9strap
- Once it is complete, press (A) to reboot your device
- Your device should have booted into the Luma3DS configuration menu
- Luma3DS configuration menu are settings for the Luma3DS custom firmware. Many of these settings may be useful for customization or debugging
- For the purpose of this guide, leave these options on the default settings (do not check or uncheck anything)
- If your device shuts down when you try to power it on, ensure that you have copied
boot.firmfrom the Luma3DS.zipto the root of your SD card
- Press (Start) to save and reboot
At this point, your console will boot to Luma3DS by default.
- Luma3DS does not look any different from the normal HOME Menu. If your console has booted into the HOME Menu, it is running custom firmware.
- On the next page, you will install useful homebrew applications to complete your setup.
Section V - Restoring WiFi Configuration Profiles
In this section, you will trigger the BannerBomb3 exploit a second time so that you can restore the Wi-Fi connection slots that were overwritten in Section II.
- Launch System Settings on your device
- Navigate to
Data Management->DSiWare->SD Card(image) - Use the D-Pad to navigate and press the (A) button to select “Uninstall unSAFE_MODE”
- Your device will automatically reboot
- Power off your device
- Insert your SD card into your computer
- Navigate to
Nintendo 3DS-><ID0>-><ID1>->Nintendo DSiWareon your SD card - Delete
F00D43D5.binfrom your Nintendo DSiWare folder and from your computer. This file will not be needed anymore