Dumping Movable (nimhax)
Technical Details (optional)
To install boot9strap on your device, we derive your device’s unique encryption key. To accomplish this, we use the Homebrew Launcher to launch nimhax and dump the data encryption key (movable.sed) from your device.
For a more technical explanation, see here for information about the nimhax exploit.
Qué necesitas
- The latest release of nimhax (the nimhax
.zipfile)
Instrucciones
Sección I - Preparativos
- Apaga tu consola
- Inserta tu tarjeta SD en tu computadora
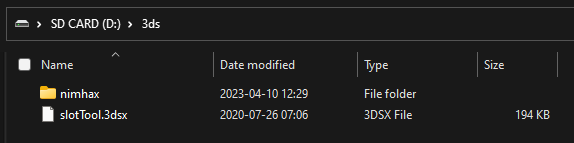
- Copy the
nimhaxfolder from the nimhax.zipto the/3ds/folder on your SD card - Reinserta tu tarjeta SD en tu consola
- Enciende tu consola
Section II - nimhax
- Open the Homebrew Launcher through your method of choice (likely the Internet Browser)
- Launch nimhax from the list of homebrew
- If the exploit was successful, a
movable.sedfile will appear on the root of your SD card
Next step: Choose an exploit
Bannerbomb3 (recommended)
Once you have your device’s encryption key (movable.sed), you can use it in conjunction with BannerBomb3, which uses your movable.sed file to take advantage of exploits in the System Settings application.
Continue to BannerBomb3
Frogtool
Once you have your device’s encryption key (movable.sed), you can use it in conjunction with Frogtool, which uses your movable.sed file to inject and take advantage of JPN Flipnote Studio.
While this method is faster, it requires downloading a file with a torrent client. Do not follow this method if you’re unable to use a torrent client.
Continue to Installing boot9strap (Frogtool)